The worm’s effects stirred several people to action. One positive outcome from this experience was development in the United States of an infrastructure for reporting and correcting malicious and nonmalicious code flaws. The Internet worm occurred at about the same time that Cliff Stoll reported his problems in tracking an electronic intruder . The computer community realized it needed to organize. System administrators now exchange information on problems and solutions.
You can repair the DLL error with the detailed guide here. A clean installation of Windows will wipe out everything from the hard drive and install a fresh copy of Windows. Run command prompt, copy and paste the following command, and press Enter. If a DLL error occurs when you open or are using a particular program, then you should reinstall the program properly and register the DLL file again.
DLL Download Sites Could Compromise Your Computer’s Security
First off, the downloaded .dll file can have malware that can infect your entire system. To top it, the downloaded version may not match the version in your operating system, and this is sure to increase your problems. It is also possible to bind an executable to a specific version of a DLL, that is, to resolve the addresses of imported functions at compile-time. For bound imports, the linker saves the timestamp and checksum of the DLL to which the import is bound. At run-time, Windows checks to see if the same version of library is being used, and if so, Windows bypasses processing the imports. Otherwise, if the library is different from the one which was bound to, Windows processes the imports in a normal way.
- If you’re a Norton user, we’ve got a dedicated guide for you to completely uninstall the antivirus.
- You can also run an executable this link file from the command line by typing its name.
- Programs that can handle DLL files are as follows.
First, will Windows NT boot its normal way without you noticing the boot virus infection? Second, if Windows NT does boot without error can boot infectors infect accessed floppy diskettes to spread even further? If Windows NT boots with an infected FAT partition and the virus doesn’t modify the partition table, chances are the boot will be successful without Windows NT noticing any changes. Even stealth routines, which in DOS would hide the virus, are nullified. And any payload damage the virus has that runs before NT has control can cause harm. Because of this, boot viruses can and do cause damage to NT systems.
Definitely do not close this page until the download begins. Our site will connect you to the closest DLL Downloader.com download server in order to offer you the fastest downloading performance. Connecting you to the server can take a few seconds. Don’t save the files to the original location to avoid further overwriting. The user can also preview the file before recovery.
Free Music Production Software
Unsolicited e-mail, normally containing advertising. These messages, usually mass-mailings, can be highly annoying and waste both time and resources. This is a program that displays pictures or animations on the screen.
Panda Security Info Glossary
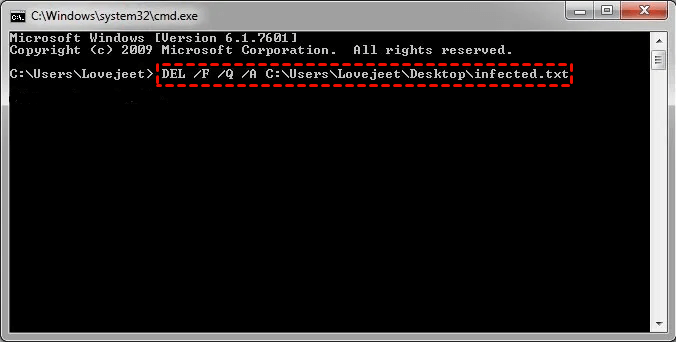
Once the Recycle Bin is empty, the error message should not appear. This, however, is a one-time solution – the error might appear again once you add files to the Recycle Bin. If you want to delete your files permanently , use the Shift + Delete keyboard shortcut or press and hold the Shift key while clicking the Delete option. In our experience, deleting files permanently helped to fix this issue.

